Firefly Remote Mount System
Background
In Firefly Cloud Phone Server, the core board cluster allows users to have multiple "real" mobile phones, but each core board needs to be installed with a fixed operating system. If you want to change the system, you need to rewrite the firmware to install the new system on the core board - the installation process is complex and takes a long time, and the user's data cannot be automatically retained.
This solution allows users to remotely mount the operating system through network, and can write back and store data through network in real time when switching or exiting the system. Users do not need to rewrite the system on the core board, which replaces the complex steps.

Introduction
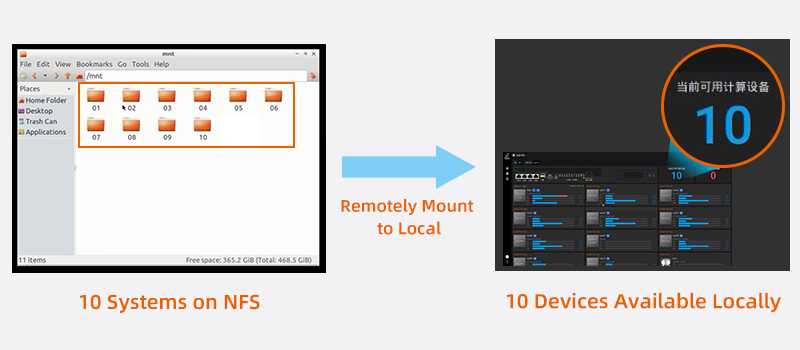
This technical solution realizes the remote mount of operating systems through NFS (Network File System).
For example, users can centrally place the system files on the NFS remote server, through this technology, the systems placed on the server can be remotely mounted and started. In this process, there is no need to flash image on local core boards, and users' data space is no longer limited by the core boards' own ROM, and at the same time, the desired operating system can be seamlessly switched to at any time.
Features
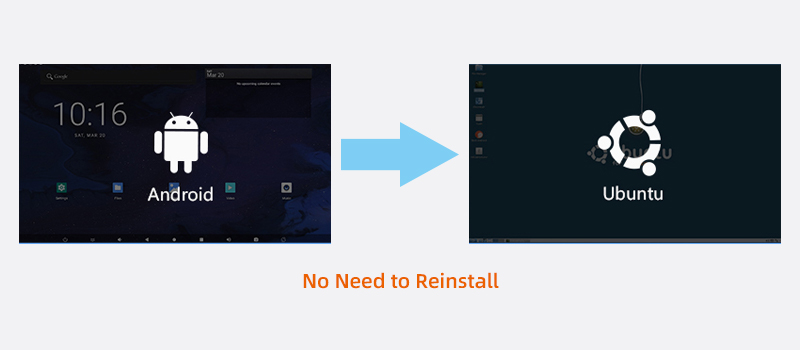
(1) Remotely mount instead of reinstalling
When users need to replace the system on the core boards, they only need to use the BMC management background to remotely mount instead of reinstalling the system, which is convenient for unified management of multiple operating systems.
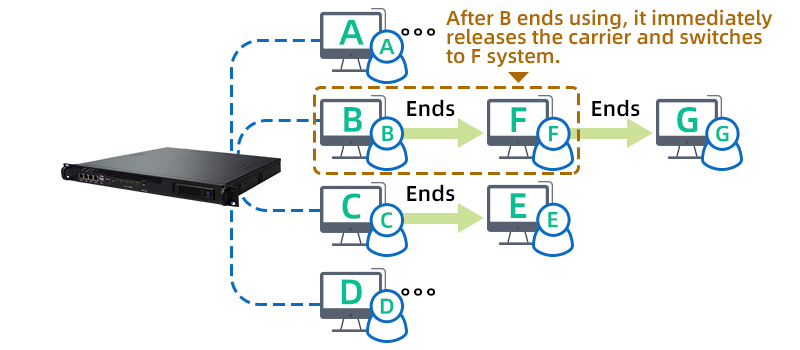
(2) Seamless system switch for more users
Through Firefly's self-developed "Seamless Switch" technology, when the hardware resources (core boards) are free, the system of the previous user can be automatically and quickly switched to the system of the next user, so the core board can be assigned to the next user. It can accommodate more users without being limited to the number of hardware resources (core boards).
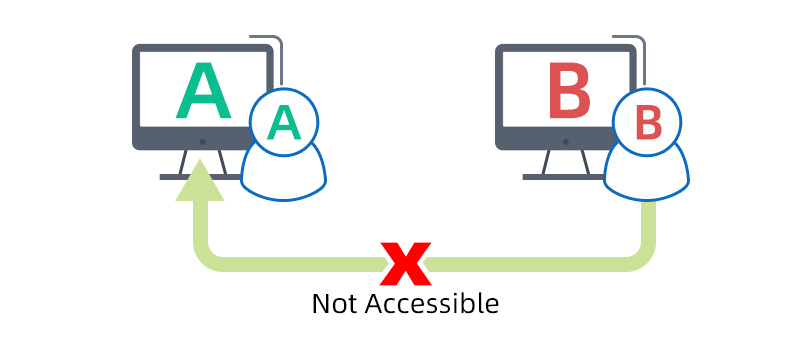
(3) Data isolation, Safe and reliable
Hardware resources and systems are not shared among users - data are completely isolated; other users cannot access and use your data, which enhances security and independence.
(4) Open interfaces, Secondary development
We provide API to facilitate the secondary development of users and to meet the application requirements of different scenarios.

Applications
It can be used in scenarios such as enterprise cloud office, data isolation of government and enterprise secret-related units, enterprise private cloud, data storage, encrypted office, online store operation, and live stream interaction.

Contact us at sales@t-firefly.com for more solutions